Xcitium Business Plans
Xcitium Essentials
- Complete Threat Prevention
- Proactive Zero Dwell Containment
- No Productivity or Business Disruption
Xcitium Advanced
- Saas Management Console
- API + Cloud-Based Updates
- Verdict Cloud Engine + ThreatIntel
Xcitium Managed MDR
- Advanced Managed Threat Solutions
- 24/7/365 Continuous Monitoring
- Threat Intelligence Integrations
Xcitium Complete M(X)DR
- Extended Detection & Response Across Endpoints
- Real-Time Response & Reporting
- Proactive Threat Hunting
Chat with a Cybersecurity Expert today!
When it comes to securing your enterprise endpoints, it's important to have an understanding of the isses.
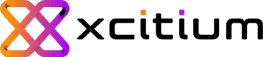
Detection-based solutions are never 100% able to determine what is harmful and what is good. Unknown files may be perfectly harmless and required for system functionality or they may be dangerous zero-day threats or APTs that cause mega breaches.
Your cybersecurity solution must be able to detect the difference to both prevent breaches and enable productivity. Xcitium’s Patented ZeroDwell Containment technology defeats zero-day attacks with no impact to the end user experience
Control Your Security Impact
A single unified endpoint solution offering exploit prevention, advanced threat hunting, and endpoint management to stop ransomware, avoid breaches, and sustain your business.
Cloud-Based Security Updates
Equip every endpoint, network, and workload with the latest threat intelligence against cyber threat signatures and payloads.
Protect Against Unknowns
Defend against new or zero-day cyber threats using powerful static, dynamic, and patented behavioral AI.
Zero-Threat
Prevent unknown cyber-attacks from causing damage to your endpoints with our lightweight Kernel-level API virtualization.
Attack Chain Visualizations
Gain full context of an attack to connect the dots on how hackers are attempting to breach your network.
Discover Endpoint Security Bundles
XCITIUM ESSENTIALS
PREVENTION
ZERODWELL CONTAINMENT
Protect against execution of all Unknown Threats with patented isolation technology.
XCITIUM ADVANCED
PROTECTION
ADVANCED ENDPOINT PROTECTION
Protect your endpoints with Anti-Virus, HIPS, Firewall, NGAV, + ZeroDwell Containment.
VISIBILITY
ENDPOINT DETECTION & RESPONSE
Gain complete visibility across your endpoints and network to provide root cause storyline enrichment.
REMEDIATION
ENDPOINT MANAGER
Attack surface reduction with patch management and remote remediation.
XCITIUM MANAGED
MANAGED
MDR
Fully Managed Service providing People, Process, and Xcitium Technology. Includes Xcitium Advanced.
XCITIUM COMPLETE
COMPLETE
XMDR
Includes MDR plus Xcitium's Network/Cloud Sensor technology for 3rd party data consumption.